As the leading Vulnerability Assessment & Penetration Testing (VAPT) in the Dubai UAE, we help you uncover vulnerabilities in your applications before attackers can exploit them. Our proactive approach identifies and mitigates threats within your systems and networks, ensuring you stay resilient and ahead in today’s rapidly evolving technological landscape with our cutting-edge penetration testing services in Dubai UAE.
Vulnerability Analysis and Penetration Testing (VAPT) is one of our most sought-after cybersecurity services in Dubai UAE, with over 90% of our Business choosing it. During the penetration testing process, we adopt the perspective of real-world hackers, thoroughly examining target systems to uncover vulnerabilities.
Penetration testing has become a critical requirement for cybersecurity services in Dubai, highly recommended for identifying application weaknesses and vulnerabilities. This team will conduct comprehensive testing on your systems and applications, following SIA (NESA), ISR, ISO 27001, ADSIC, CREST, ADHICS, and PCI DSS compliance requirements, utilizing the most effective cybersecurity strategies and industry-standard tools.

Our Penetration Testing services in the Dubai UAE have been meticulously designed after consulting with leading app providers across various sectors, including SaaS, Fintech, HealthTech, E-commerce, startups, and web and mobile app development companies. This tailored approach ensures that your business is safeguarded against every potential cyber threat.
The standard process of a VAPT engagement includes the following steps and tools.
Our VAPT Service employs a comprehensive, advanced security testing methodology that thoroughly examines the internal workings of your applications and network configurations, identifying critical issues, exposure points, and business logic flaws. By combining automated and manual testing, we uncover security vulnerabilities while eliminating false positives, ensuring every aspect of your application’s and network’s security is rigorously assessed.
We begin each project by understanding the business logic, workflows, and architectural designs of your applications and networks.Our expert team utilizes cutting-edge automated technology to detect vulnerabilities, leaving no detail unchecked. Additionally, we personally verify each result for unparalleled accuracy.
VAPT services enhance the security of your company by fixing and identifying vulnerabilities. Improve testing process is crucial that an organization has a better understanding of the services included in VAPT before beginning the program:
A vulnerability assessment involves vulnerability scanning and is designed to detect, categorize, and address security threats. Additionally, vulnerability assessment services offer the continuing guidance and support required to effectively mitigate any risks identified.
Vulnerabilities may exist in operating systems, services and application flaws, improper configurations, or risky end-user behavior. Penetration test is a comprehensive vulnerability assessment identify vulnerabilities that integrates human-led techniques with an advanced-tech enabled approach to test for vulnerabilities.
Red team operation is a cyber attack simulation exercise conducted to check on the attack preparedness of an organization. A real-world environment is simulated using cutting-edge hacker techniques and strategies in this security assessment, which goes beyond the typical VAPT.
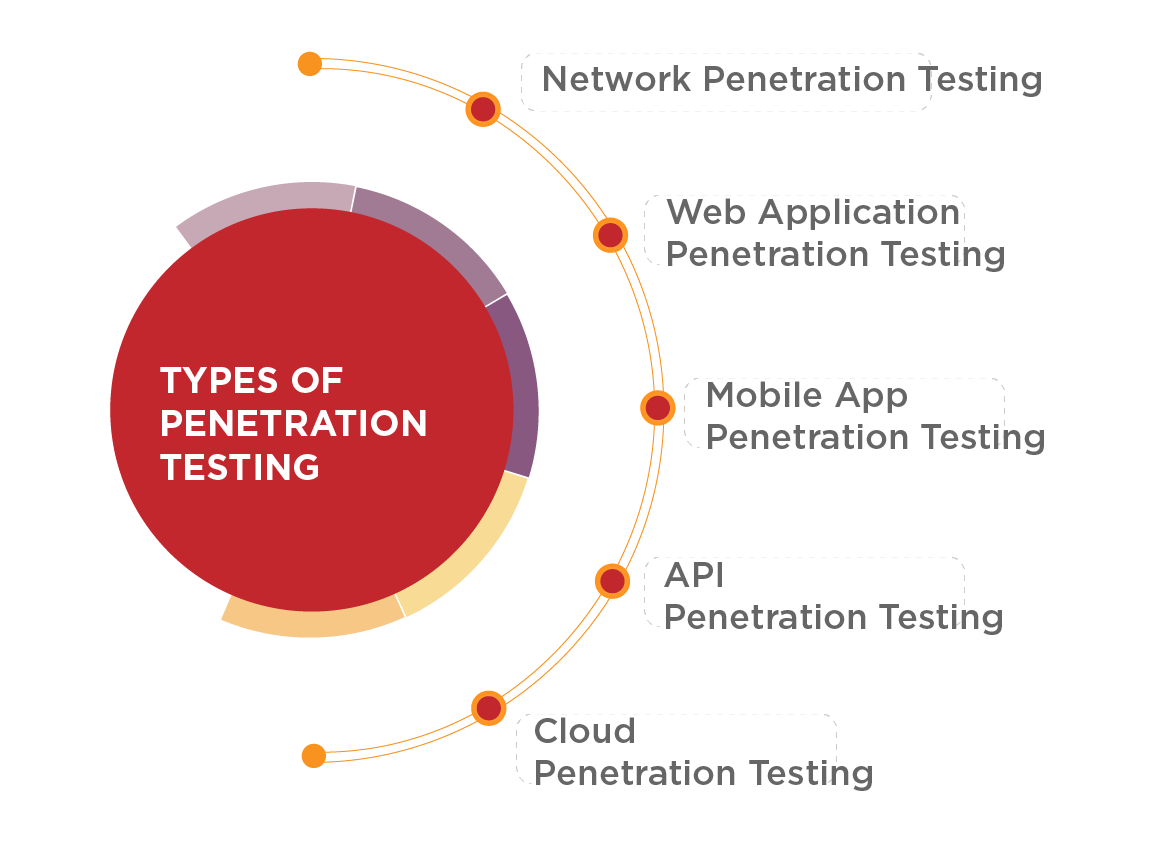
Penetration testing comprises various specialized assessments designed to evaluate and strengthen the security of computer systems. Each type plays a crucial role in ensuring robust cyber Security and safeguarding organizations from potential threats.
A penetration testing company in the UAE, we find and fix vulnerabilities in your applications before attackers can exploit them. Our services help you stay secure by proactively identifying and addressing threats in your systems or networks, ensuring you’re always a step ahead in the evolving tech landscape.

Suggested for businesses that create mobile-based applications for games, payments, shopping, and more before they are made available to the general public.
Perfect for cloud-based organisations and networking companies that relay large amounts of data.
The most popular and necessary sort of pentest for businesses with any web assets.
Companies that use an API backend in their web or mobile applications must regularly conduct API pentests to protect themselves from exposure or incorrect coding.

It is necessary for businesses that offer cloud services like AWS, Google Cloud Platform, Azure, and cloud security services.
VAPT is considered the most effective method for identifying potential security risks and resolving an organizations security weaknesses. With the advanced malware and hacking techniques used by hackers, and the alarming rate of increasing cyber attacks (up to a 70% increase from 2021).
VAPT has become critical for businesses and organizations in the UAE. VAPT simulates a hacker attack to gain 360-degree visibility into organizational vulnerabilities and assists in meeting compliance standards such as GDPR, PCI DSS, and ISO 27001.
Look no further than Mechsoft Technologies. With our expertise and experience, we are the go-to choice for VAPT testing in Dubai, UAE. Our team of skilled professionals is equipped with the latest tools and techniques to identify and rectify potential vulnerabilities in your systems, ensuring optimal cyber security services.
We follow a comprehensive approach that covers network security, application security, and data security.Mechsoft Technologies, you can rest assured that your organization’s digital assets are protected from potential threats. Trust us to provide you with reliable and effective VAPT testing services in Dubai, UAE & Middle East.
VAPT Testing, which stands for Vulnerability Assessment and Penetration Testing, is a security testing process designed to identify vulnerabilities in a system or network and evaluate its resilience against attacks. This process includes both automated scanning to detect vulnerabilities and manual testing to exploit them.
VAPT is crucial because it enables organizations to identify weaknesses in their systems or networks before they can be exploited by malicious attackers. It allows businesses to proactively address security vulnerabilities, enhance their defenses, and safeguard sensitive data and resources from unauthorized access through comprehensive VAPT service approaches.
A security assessment identifies potential weaknesses in an application, while penetration testing explores how severely those vulnerabilities can be exploited by a malicious attacker.
A standard penetration test typically ranges from $10,000 to $30,000, though in some cases, it can be as low as $1,000.
We utilize a controlled environment, appropriate encryption standards, and various anonymization techniques to carefully manage your data during penetration testing, tailored to its level of sensitivity.
We provide a comprehensive range of services including Web Application Security Assessment, Mobile Application Security Assessment, Network Security Assessment, API Security Assessment, Operational Technology Security Assessment, IoT Security Assessment, Secure Code Review, Annual Security Programs, Approved Scanning Vendor services, WordPress Security Audit & Assessment, Cloud Application Security Assessment, Wireless Penetration Testing, Security Architecture Review, Managed Threat Hunting, Device Security Audit & Assessment, Red Teaming, Purple Team Assessment, ERP Security Audit, Email Security Audit, and SCADA Vulnerability Assessment and Penetration Testing (VA/PT).
Relying on local penetration testing service providers allows you to customize your security measures according to the specific cybersecurity threats and landscape of your region. It also helps you uncover unique and specific security challenges relevant to your area.
Security professionals and organizations worldwide recommend conducting penetration testing at least once a year.
Yes, we offer post-penetration testing support and assistance with remediation efforts for identified vulnerabilities in the UAE.