Protect your industrial operations with trusted OT Cybersecurity Solutions in Dubai, UAE. Secure SCADA, PLCs, control systems, and critical infrastructure from cyber threats, downtime, and operational risks. Our tailored services help improve resilience, ensure compliance, and maintain safe, uninterrupted operations across industrial environments.
In today’s industrial landscape, operational continuity is critical. As Information Technology (IT) and Operational Technology (OT) environments become increasingly connected, industrial systems are becoming more exposed to sophisticated cyber threats. Mechsoft Technologies delivers specialized OT Cybersecurity Solutions designed to secure SCADA systems, ICS environments, industrial networks, and critical infrastructure without disrupting operations.
Our integrated OT security ecosystem helps organizations strengthen resilience, maintain operational safety, and ensure uninterrupted industrial performance.
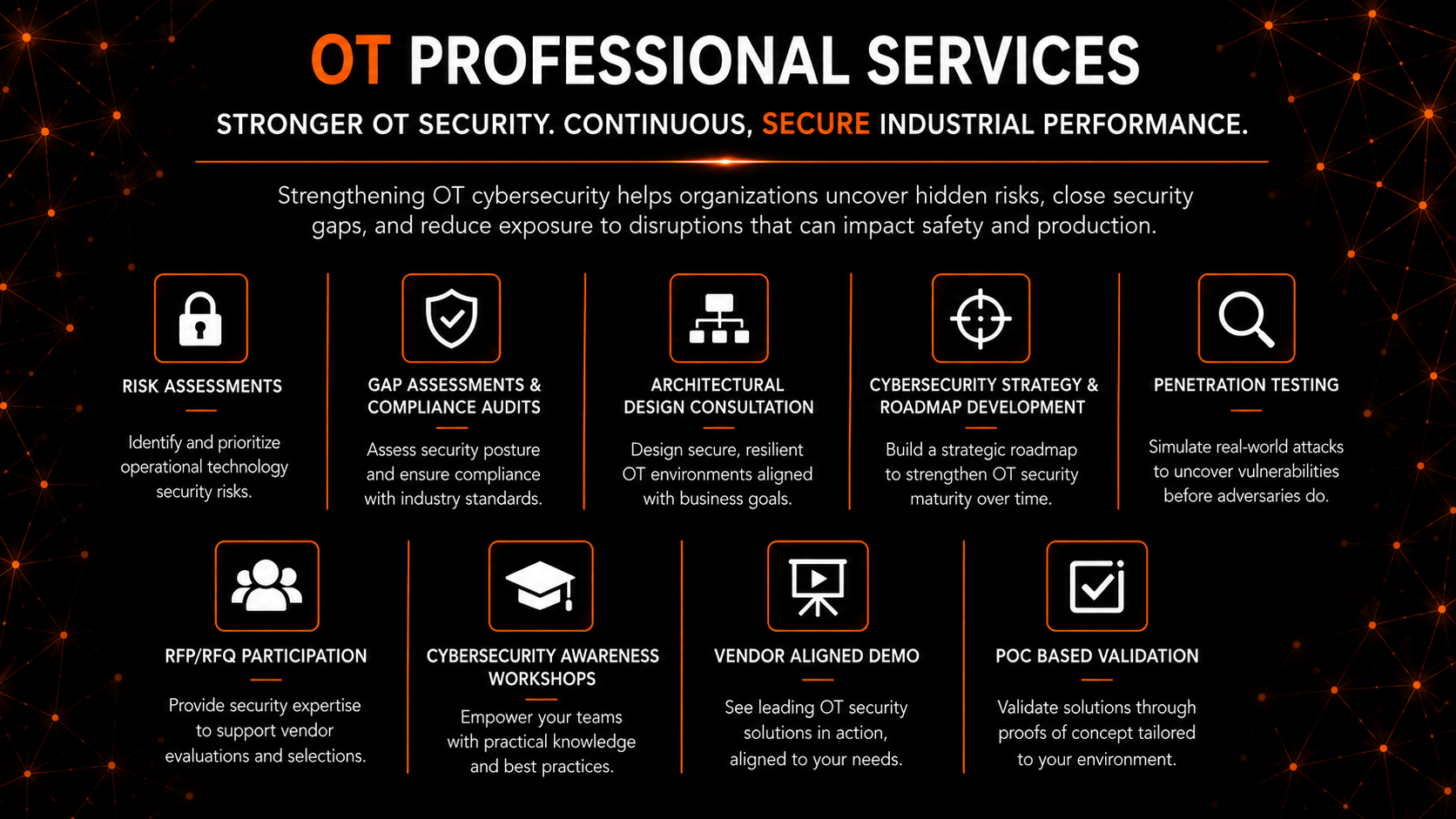
Traditional IT security strategies are not designed for industrial environments. OT systems operate differently, with unique priorities such as uptime, operational safety, and long equipment lifecycles. Industrial environments require specialized cybersecurity controls that protect critical operations while ensuring stability and availability.
| Feature | Traditional IT Security | Mechsoft OT Cybersecurity Solutions |
|---|---|---|
| Primary Goal | Data confidentiality | Operational availability and safety |
| Maintenance Approach | Frequent patching and reboots | Minimal disruption and continuous operations |
| System Lifespan | Short lifecycle infrastructure | Long lifecycle industrial and legacy systems |
| Impact of a Breach | Data loss and privacy risks | Operational shutdowns and physical safety risks |
Industrial organizations must also address growing risks from ransomware, insider threats, remote access vulnerabilities, and unmonitored legacy systems. A dedicated OT cybersecurity strategy ensures these environments remain protected without affecting production processes.
Continuously identifies and maps industrial devices including PLCs, HMIs, SCADA systems, sensors, and controllers across the environment.
Detects vulnerabilities and high-risk assets without interrupting industrial operations or production processes.
Monitors OT traffic and behaviors to identify suspicious activities, unauthorized changes, and abnormal communication patterns.
Separates critical industrial environments from corporate IT networks to reduce lateral movement and limit cyber exposure.
Provides controlled and monitored access for engineers, vendors, and third-party operators connecting to industrial systems.
Deploys decoy assets and fake industrial systems to detect and divert attackers before they reach production environments.
Controls user and device access to industrial systems based on roles, policies, and operational requirements.
Provides a unified dashboard for monitoring industrial assets, threats, vulnerabilities, and compliance status.
Delivers continuous monitoring and intelligence to identify emerging threats targeting industrial sectors.
Supports rapid containment and recovery with OT-focused incident response planning and playbooks.
Mechsoft Technologies follows a structured and objective-driven approach to strengthen industrial cybersecurity.
| Phase | Objective | Key Deliverable |
|---|---|---|
| Assess | Identify critical industrial assets and risks | Comprehensive OT asset and risk assessment |
| Protect | Build secure industrial network boundaries | Segmentation, firewalling, and access control |
| Detect | Continuously monitor industrial activity | Real-time threat detection and monitoring |
| Respond | Enable rapid recovery and resilience | OT incident response and recovery planning |
Mechsoft Technologies delivers specialized expertise in securing industrial environments across sectors such as manufacturing, utilities, oil and gas, logistics, and critical infrastructure.
Our OT cybersecurity approach focuses on protecting industrial operations while maintaining uptime, safety, and reliability. We help organizations secure both modern and legacy industrial systems through advanced monitoring, segmentation, access control, and threat detection capabilities.
OT cybersecurity focuses on protecting industrial systems, operational technology environments, and critical infrastructure from cyber threats while ensuring operational continuity and safety.
OT security prioritizes operational availability, safety, and system reliability, whereas traditional IT security primarily focuses on protecting data confidentiality and business applications.
Yes. OT security solutions are designed to secure both modern and legacy industrial systems, including environments where patching or upgrades are limited.
Segmentation isolates industrial systems from external networks and reduces the risk of attackers moving laterally between environments.
Modern OT security solutions are designed to operate with minimal disruption and without impacting critical industrial processes.
Industries such as manufacturing, utilities, oil and gas, transportation, logistics, healthcare, and critical infrastructure benefit significantly from OT cybersecurity solutions.
Content